In a bewildering mess, a recent Microsoft Defender update rolled out a new stability feature known as ‘Kernel-mode Hardware-enforced Stack Defense,’ even though removing the LSA defense element. Sad to say, Microsoft has not offered any documentation on this modify, main to additional issues than answers.
Nearby Security Authority Defense, aka LSA Safety, is a protection attribute that safeguards sensitive information and facts, like qualifications, from remaining stolen by blocking untrusted code from becoming injected into the LSASS procedure and LSASS procedure memory dumping.
Home windows buyers can empower LSA Safety in the Windows Security > System Security > Core Isolation configurations website page for CPUs that assistance virtualization.
However, for the earlier few months, Windows 11 people have complained that they cannot permit the Area Security Authority Protection security function in the Home windows Protection ‘Core Isolation’ options.
When making an attempt to do so, Home windows prompts buyers to restart the computer system to help the feature, but on reboot, it would not be enabled, and Home windows would as soon as once more exhibit a reboot prompt.
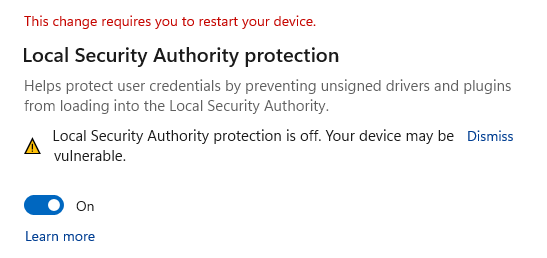
Microsoft afterwards explained that if you experienced enabled LSA Protection and restarted your system at the very least once, you could dismiss these warnings.
A workaround was also supplied to check if LSA Security is enabled and how to configure two Registry keys to disable the warning.
Microsoft Defender update generates confusion
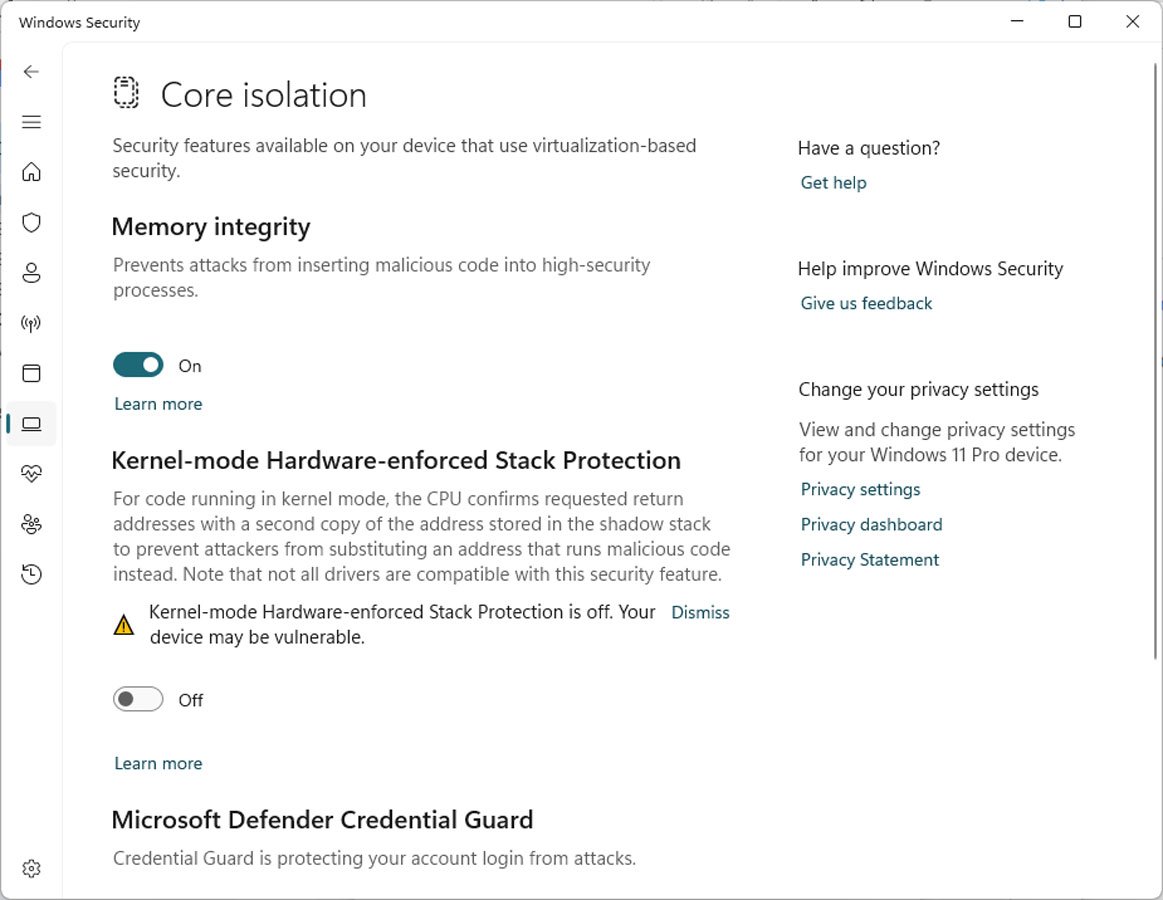
A recent Microsoft Defender update has built this characteristic even additional bewildering, as soon after it is put in, the LSA Protection element is removed and changed by a new function called Kernel-method Components-enforced Stack Defense.
Kernel-mode Components-enforced Stack Security is a protection element that makes an attempt to reduce ROP (Return Oriented Programming) centered management flow assaults that could direct to code execution.
“For code operating in kernel mode, the CPU confirms asked for return addresses with a second duplicate of the handle stored in the shadow stack to stop attackers from substituting an deal with that operates destructive code instead,” explains the Windows Kernel-mode Hardware-enforced Stack Safety environment.
“Observe that not all drivers are appropriate with this security aspect.”
On the other hand, to use this characteristic, a Windows gadget should be making use of Intel Tiger Lake CPUs or AMD Zen3 CPUs and afterwards. For that reason, Home windows will only display screen this new placing if the device has the expected hardware.
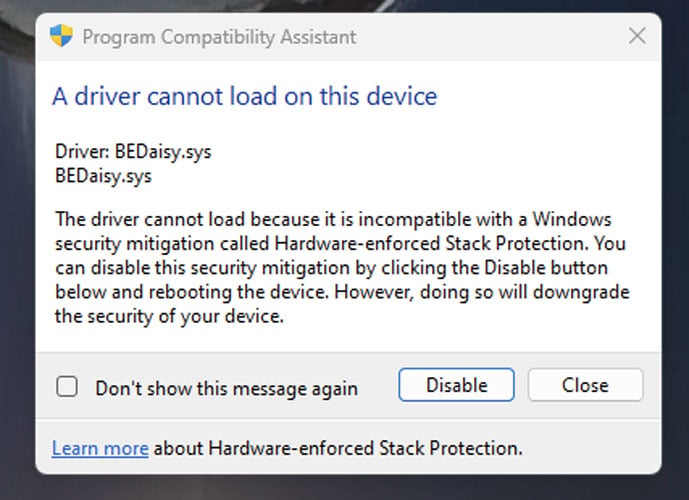
Like Memory Integrity, when enabling Kernel-method Components-enforced Stack Defense, Home windows will ensure that no incompatible motorists are loaded in Home windows. If there are, the Stack Protection function will not permit, and Windows will screen a checklist of incompatible drivers.
Windows 11 buyers now report looking at Windows safety notifications that the new function is disabled because of to conflicting drivers.
“Kernel-manner Components-enforced Stack Protection is off. Your device may well be vulnerable,” reads a warning in the Home windows Stability Centre.
Source: BleepingComputer
Even so, when they examine the list, it is vacant, producing it baffling how to empower the feature.
Even even worse, some conflicting match anti-cheat motorists are not detected as incompatible, and Kernel-manner Hardware-enforced Stack Security is continue to enabled. These conflicting motorists are producing Windows to crash or for online games not to run when the security function is enabled and a activity is launched.
Home windows 11 consumers have claimed these problems for PUBG, Valorant (Riot Vanguard), Bloodhunt, Future 2, Genshin Effects, Phantasy Star Online 2 (Sport Guard) and Dayz.
Supply: Reddit
What occurred to LSA Security?
Even extra irritating is that Home windows 11 people can no for a longer period enable LSA Protection, which did not involve more recent CPUs, from the Windows Security configurations.
It really is not even very clear if LSA security is bundled into the Kernel-mode Components-enforced Stack Defense or has been taken off from the Home windows Environment interface solely, requiring people to allow it manually by way of the Registry.
In addition, there has been no notice from Microsoft about the swapping of these security functions or about Kernel-mode Hardware-enforced Stack Defense becoming added other than the temporary description found in Home windows Safety and the scattered documentation [1, 2, 3] on the Stack Protection characteristic.
BleepingComputer asked Microsoft about the new Stack Safety attribute if LSA Security is now bundled within it, and the conflicts folks are owning.
This article will be current with any responses we get.